
Intelligent Protection International Limited - Providing over a decade of security and protection for our global clients!
Security Audits & Security Reviews
“Security audits and reviews are a balance between possible threat, financial loss and the cost of security”
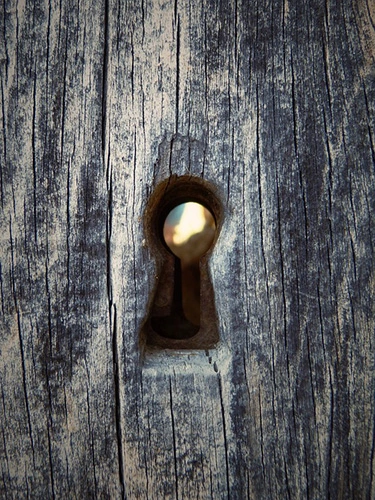
What is a Security Audit?
A security audit is a periodic methodical evaluation of the security of a company or organisation by measuring how well it conforms to a set of established criteria. This criteria that is normally agreed in advance, will cover both technical and physical security as well as open source intelligence.
 It does not matter how good you think your physical or technical security is, only by periodic security audit will you obtain a high standard of security aided by workable policies.
It does not matter how good you think your physical or technical security is, only by periodic security audit will you obtain a high standard of security aided by workable policies.
Security Audits Identify Exploitable Weaknesses
Exploitable weaknesses come in different guises. They are points of failure that on their own or together leave businesses and organisations exposed. These exploitable weaknesses maybe technical such as your IT systems, access control or alarms, physical such as your policies and procedures, on-site security guards, window locks etc. or they may be information that is posted online that can be used against you.
Intelligent Protection International Limited will look at how ALL of your security work together. We provide a full and cost-effective security audit to enable the best possible security to be provided, based on sound practice and the experience of members of our team. Our security audit service is designed to mitigate risk and to identify areas of weakness that could be exploited by the likes of hackers of organised criminals. The audit reports we produce will enable clients to make investment in the right areas.
These days, many company executives often work from home or other remote locations that are often not a secure environment to conduct company business or to discuss important business transactions. This dynamic needs a different approach, and this is where policy and good practice needs to be implemented through training.
If you cannot get your people to 'buy-in' to your security policies because they are too complex, then you are on a non-starter.
“Every great security policy will start with a difficult conversation” - Alex Bomberg
Adapting Security Audits for Growing Businesses
Reviewing your security and modelling the threats, including internal policies should be part of your ongoing business development, changing as your business grows. We work with clients, many of whom are starting from afresh with either little or no security policies adopted. This is common place and a review of your business and its procedures will identify what you need and what you do not.
As part of any review, we will work with your management to review your internal policies to ensure that they are within current legal guideline, understood by the workforce and that they are workable. Our security review covers both Insider Threat and External Threats, from risk of petty theft through to how an act of terrorism or espionage might affect your business.
Reviewing your security
Our vast experience over different security disciplines enables us to look at where you might be exposed. Every client is different and have specific threats. Our 'root and branches' approach enables us to look at almost every eventuality, mitigating the threats, from soft easy options to more complicated IP theft, or acts of terrorims or espionage.
A dedicated physical & technical security review and penetration testing will often seek to exploit reduced levels of security at these areas to gain important information. A Technical Surveillance Countermeasures or TSCM Sweep Service, should also include any such global satellite office locations.
One area that we seek to develop is your Major Incident Management Plan (MIMP), again to ensure it is fit for purpose. Protecting and preparing your firm against acts of terrorism has been the subject of one of our recent blog articles: Protecting a Business Against Terrorism.
Please contact us to discuss any requirements that you might have or to answer any question regarding this service.
Our Security Audit services cover:
- Full Physical Security Review
- Policy and Procedure Review
- Physical Penetration Testing
- Computer & IT Security Review
- Technical Penetration Testing
- Staff Training
- Open Source Intelligence
- Technical Surveillance Countermeasures (TSCM)

